When Vendor Sprawl Becomes Structural Risk
The average enterprise data breach now costs $4.4 million. According to IBM’s 2025 Cost of a Data Breach Report, third-party vendor involvement is consistently among the top contributors to breach severity, not because of sophisticated attacks, but because of access that was never revoked, and tools that were never reviewed.
This is a governance problem. And for most mid-to-large enterprises, the current approach to vendor oversight – a combination of spreadsheets, manual tracking, and institutional memory is not a control system. It is a liability posture with a time delay.
The gap between the vendors you think you’re managing and the vendors that are actively operating inside your systems, processing your data, and renewing your budgets has a name: vendor sprawl. The cost of ignoring it is no longer theoretical.
Three Ways Unmanaged Vendors Are Costing You Now
1. The Security Exposure
Third-party vendor relationships are now one of the primary vectors for enterprise data breaches. The risk is rarely a sophisticated external actor. More often, it is a deprovisioned contractor whose credentials were never revoked, or a forgotten API key sitting in a system without monitors.
The math is unambiguous. If a vendor in your ecosystem holds access to customer data and that vendor’s security posture is weaker than yours, your breach exposure is effectively that vendor’s exposure. That is not a metaphor. It is the documented mechanism behind some of the most expensive breach events in recent enterprise history.
2. The Compliance Time Bomb
Regulatory frameworks have stopped giving enterprises the benefit of the doubt on third-party risk. The EU’s Digital Operational Resilience Act (DORA), which came into force for financial institutions in January 2025, makes this explicit: you are responsible for the resilience of your vendors, not just your own systems. Financial institutions are now required to maintain registers of all ICT third-party service providers, conduct regular risk assessments, and demonstrate active monitoring, not passive vendor lists.
GDPR operates on the same accountability model. If a vendor you trusted with customer data experiences a breach, you are the data controller. The liability is yours. The fine is yours. “We didn’t know they were storing data in an unsecured environment” is no longer a legal defense. It is a board-level duty-of-care failure.
3. The Operational Drag Multiplier
Unmanaged vendors do not just introduce risk. They systematically slow down execution across the enterprise.
Every vendor engagement such as, onboarding, contracting, risk review, procurement approval, renewal becomes a fragmented, manual workflow when there is no centralized system of control. What should be a linear process turns into a multi-week coordination loop across Legal, Procurement, Finance, and IT.
At scale, this creates a compounding effect. What looks like a process inefficiency is, in reality, an enterprise-wide velocity constraint.
And unlike one-off operational issues, this drag compounds. Every additional vendor increases the number of approval paths, stakeholders, and failure points. Without centralized orchestration, vendor management does not just become complex.
It becomes a structural bottleneck to growth.
Spreadsheets Were Built for Data. Not for Live Risk
A spreadsheet does not know when a vendor auto-renews at 3 a.m. It does not flag when an employee signs up for a new tool using a corporate card. It does not update when a vendor’s compliance certification lapses, or when an offboarded employee’s access to a third-party system was never revoked.
As the BCM Institute distinguishes in its analysis of operational resilience and third-party risk management, operational resilience is not a one-time assessment, it is a continuous capability. A spreadsheet is a snapshot. Your vendor ecosystem is a living system, with new tools onboarded weekly, contracts renewing on rolling cycles, and access permissions proliferating across business units that often have no visibility into what the next unit is using.
| The Schellman whitepaper on supply chain risk management frames this precisely: for many organizations, the absence of a consistent assurance framework for evaluating third parties has replaced informed oversight with blind trust. When a governance failure can be traced to a vendor you knew you lacked visibility into, “we didn’t have a system” is not a defense. It is evidence of negligence. |
The Shift from Vendor Management to Vendor Governance
There is a meaningful distinction between managing vendors and governing them. Management is periodic. Governance is continuous. Management answers the question: what vendors do we have? Governance answers: what is happening across our vendor base right now?
A real vendor governance system identifies shadow IT the moment a corporate card is used on an unsanctioned tool. It tracks contract renewal timelines and flags lapsed certifications before they become compliance gaps. It monitors access permissions across the full vendor lifecycle and generates audit-ready records that can be presented to a regulator without a two-week scramble. Most critically, it replaces reactive damage control with the operational visibility that makes reactive damage control unnecessary.
The resilience ROI is not abstract. Gartner’s analysis finds that organizations implementing centralized SaaS lifecycle management are five times less susceptible to cyber incidents linked to SaaS misconfiguration or incomplete access visibility. Prevention is not just preferable, it is measurably cheaper than recovery.
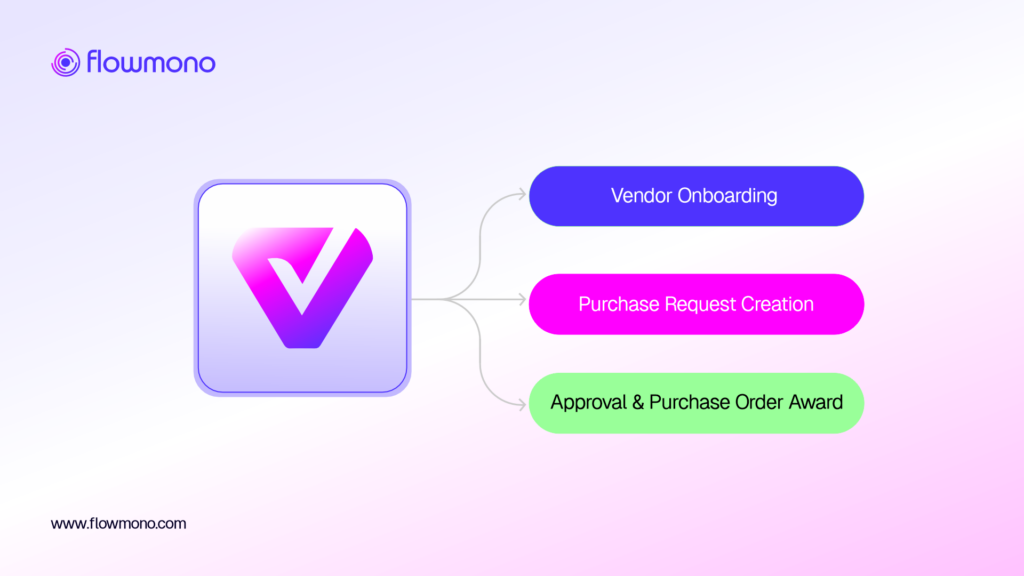
This is the governance model that Flowmono’s Vendor Procurement Management Cloud is built around: replacing static vendor lists with active, continuous governance across the full vendor lifecycle from onboarding through contract renewal, access management, compliance monitoring, and off-boarding. The platform turns vendor oversight from a quarterly exercise into a real-time operational capability.
The Right Question to Ask at Your Next Board Review
The rapid expansion of AI agents, point solutions, and decentralized SaaS procurement is adding new vendors to enterprise stacks faster than most governance teams can review them. Every tool that bypasses procurement is a new risk entry point. Every unmonitored renewal is a quiet budget drain. Every unreviewed access permission is a potential breach vector.
The Billion-Dollar Blind Spot is not shrinking. And the enterprises that will absorb the most risk in the next two years are not the ones that lack technology. They are the ones that still believe a vendor list is the same thing as a control system.
Ready to see what full vendor governance looks like in practice?
Request a demo of Flowmono VPMC and turn your largest operational blind spot into a competitive governance advantage.
![]()